Unauthorized Intrusion: Chinese Cybercriminals Capitalize on Prevalent smartphone Weaknesses
In today's interconnected world, smartphones have become indispensable tools, serving as personal assistants and digital vaults. However, their widespread adoption has also attracted unwanted attention from cybercriminals, with attacks posing a global threat, not just limited to China.
These attacks can have far-reaching consequences, as one gap in security on a single device can cascade, affecting networks on a broader scale. Cybersecurity experts warn about the increasing risks and provide insights into preventative measures.
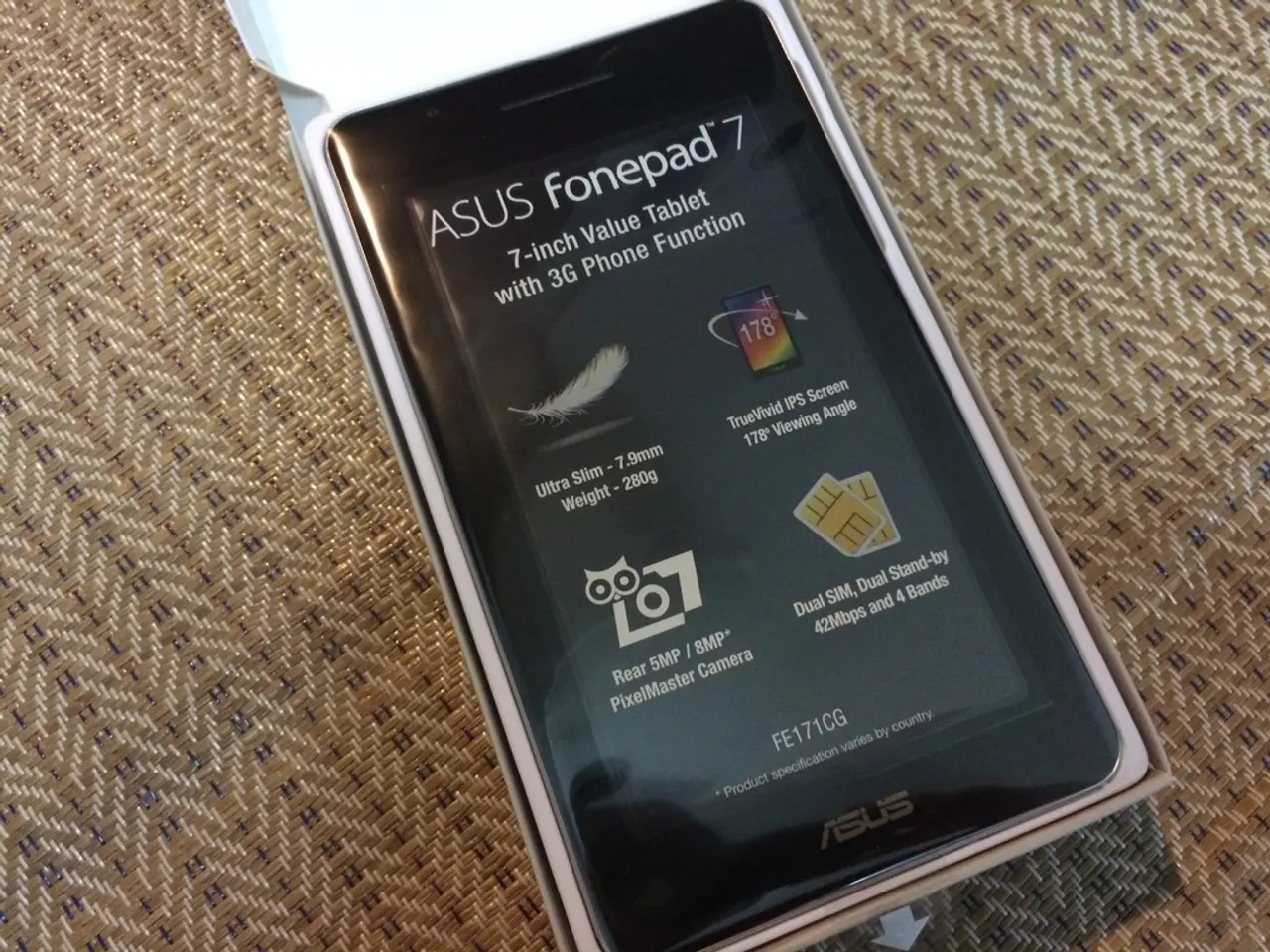
For users, keeping devices updated with the latest patches is crucial. Manufacturers like Google regularly fix critical vulnerabilities, such as the Android August 2025 patch that resolved remote code execution risks. Practicing good security hygiene, including using strong, unique passwords and avoiding clicking suspicious links, can also help prevent social engineering attacks and phishing. Enabling and maintaining critical security features, such as biometric or multifactor authentication, is also essential.
Experts also advocate for stringent measures such as enhanced encryption, proactive security patches, and comprehensive public education initiatives. Professor Elaine Zhang comments, "Software can be updated automatically; we can't say the same for human habits. That's where continuous education comes into play, pairing technological solutions with informed user practices."
For developers, regularly updating and patching software components is vital. This includes Android frameworks and third-party SDKs, which often introduce implicit trust and data leakage risks. Conducting comprehensive security testing beyond traditional audits is also necessary to address new risks from logic flaws, integrations, and behaviors in modern app architectures.
Policymakers have a crucial role to play as well. Mandating timely application of security patches for government and public-sector devices is essential, as is strengthening regulatory frameworks around data privacy and mobile security compliance. Promoting guidelines requiring segmentation between personal and professional communications on mobile devices used in government or enterprise contexts can also reduce attack surfaces.
Anne Roberts, a cybersecurity analyst, remarks, "It's a multifaceted challenge, one that requires a coordinated, multi-layered approach. Everyone from the average user to the largest corporations has a role to play." With an estimated 7.33 billion mobile users worldwide, a ripple effect of security breaches could potentially disrupt technological ecosystems globally.
As stakeholders across the spectrum grapple with these realities, proactive adaptation and resilience are critical in navigating a world defined by innovation and intrigue. The emerging landscape of mobile security underscores an unyielding truth: convenience must never come at the expense of vigilance.
- In the realm of data-and-cloud-computing and technology, encryption plays a significant role in safeguarding sensitive information on smartphones, given their function as digital vaults.
- Cybersecurity experts emphasize the importance of keeping up with the latest encryption technologies as a crucial preventative measure against cyber threats, as one gap in encryption can lead to widespread consequences.
- Encyclopedia entries on cybersecurity often discuss the role of gadgets like smartphones in attracting unwanted cybercriminal attention and the need for enhanced encryption to mitigate growing risks.
- As governments and tech companies collaborate to strengthen cybersecurity, proactive measures such as implementing new encryption standards and educating users about data-and-cloud-computing risks become essential components of a comprehensive security strategy.